7 Shocking Fixes for the 2579xao6 Code Bug (2026 Guide)

Software failures rarely appear at convenient moments. A developer finishes deployment, traffic starts flowing, and suddenly a strange string shows up across logs and dashboards. The 2579xao6 code bug has become one of those frustrating problems teams keep reporting during backend integrations, cloud migrations, and API deployments.
We have seen engineers panic when this bug pops up because it often looks mysterious at first glance. Systems slow down, error messages multiply, and the debugging process gets messy fast. Yet the truth is simple: most instances of this error follow predictable patterns, and with the right steps it can be fixed quicker than many expect.
Below we walk through seven powerful fixes that have repeatedly solved the 2579xao6 code bug in real environments. Some of them might surprise you. Some will feel almost embarrasingly simple. But each one has rescued projects that looked ready to collapse.
What Triggers the 2579xao6 Code Bug?
Before jumping to solutions, we need to identify the patterns behind this bug. In most cases, it appears when systems fail to handle a mismatched runtime dependency or when an API layer miscommunicates with the database engine.
Developers sometimes assume the problem lies inside their application logic. Actually the fault is often deeper in the environment configuration. Memory allocation limits, outdated libraries, or corrupted session tokens can trigger the 2579xao6 code bug across multiple services.
Teams researching debugging methods often review materials from reputable sources such as the MDN debugging guide, which outlines structured approaches to tracing runtime errors. Even experienced programmers forget the basics when pressure builds.
And pressure does build. When a production server start throwing errors every few seconds, people start changing things quickly. Too quickly sometimes. That usually makes the situation worse, not better.
Fix #1 Reset Environment Variables Immediately
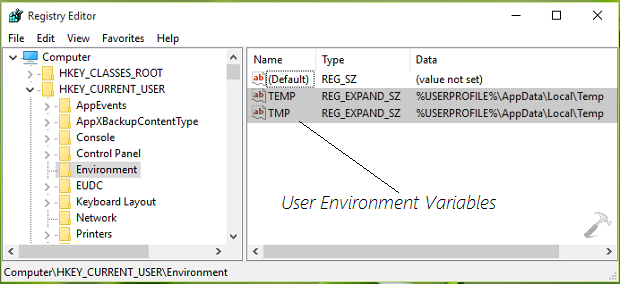
One of the most common triggers of the 2579xao6 code bug involves corrupted or conflicting environment variables.
A server might store outdated credentials, legacy endpoint URLs, or deprecated configuration keys. When the application attempts to initialize services using those invalid values, the system fails and throws the error.
Steps we usually follow:
- Audit every environment variable used by the service.
- Compare them against the latest configuration documentation.
- Remove unused variables completely.
- Restart the runtime container.
Many engineers skip step three and thats a mistake. Old variables sometimes override new values silently. Removing them entirely prevents that hidden conflict.
Fix #2 Recompile Dependencies With a Clean Build
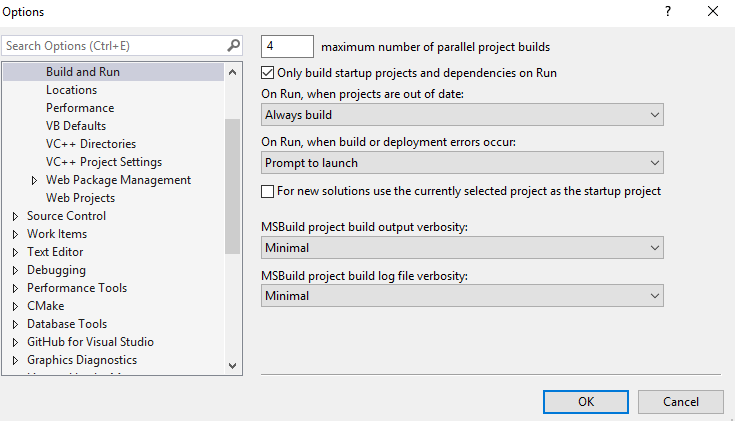
Dependency conflicts create a surprising amount of chaos. When libraries compile against mismatched versions, internal functions may return unexpected values that produce the 2579xao6 code bug.
A clean rebuild solves many cases.
Run these actions:
- Delete the dependency cache.
- Remove build artifacts.
- Install packages again from scratch.
For JavaScript ecosystems, this usually means clearing node_modules and reinstalling packages. Detailed instructions can be found in this npm installation documentation.
Developers often forget how fragile dependency trees really are. One outdated plugin can cause dozens of secondary failures. The error looks complicated but the solution sometimes is very basic.
Fix #3 Inspect API Gateway Logs Carefully
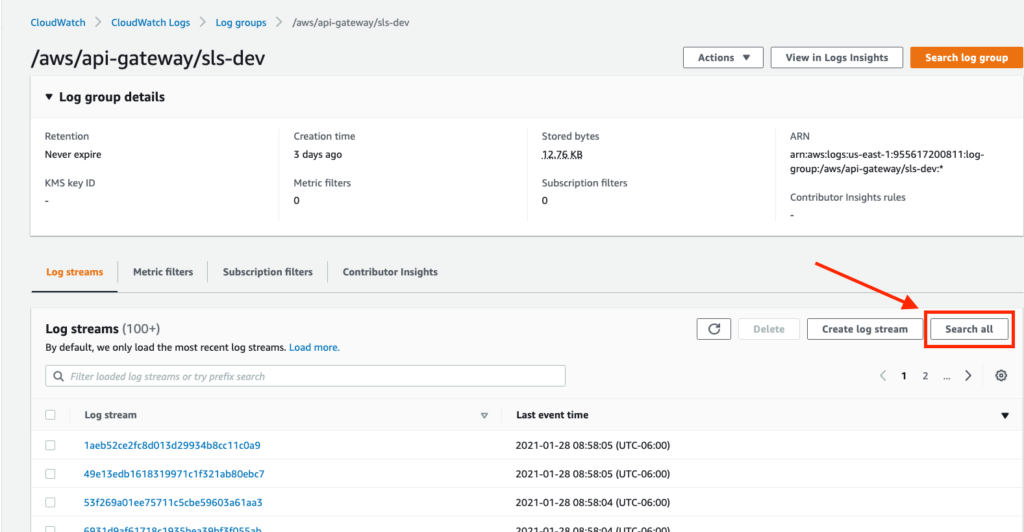
The 2579xao6 code bug often appears when an API gateway fails to validate requests correctly. The backend receives incomplete payload data, attempts processing, then crashes.
Instead of scanning application logs first, we recommend starting with the gateway logs. They reveal rejected headers, malformed tokens, or incorrect request formatting.
Look for signs like:
- Invalid authentication signatures
- Expired request timestamps
- Payload size exceeding limits
Many engineers overlook this stage and go straight into database debugging. That wastes hours and create unnecessary confusion.
Fix #4 Database Index Corruption Repair
A damaged database index can quietly trigger the 2579xao6 code bug when queries fail to resolve records properly.
When the query planner expects a valid index but encounters corrupted metadata, the application layer sometimes interprets the result as a runtime failure.
Database administrators usually fix this by rebuilding indexes. Guides like the PostgreSQL REINDEX documentation describe how to repair them safely.
However many teams forget to schedule maintenance windows before doing this. Running heavy reindex operations during peak traffic could cause additional downtime.
Fix #5 Runtime Memory Allocation Adjustment
Memory limits inside container environments can also trigger the 2579xao6 code bug. When a service approaches its memory ceiling, garbage collection behavior becomes unpredictable.
Applications suddenly fail during request processing.
We recommend monitoring memory usage closely through system diagnostics. The Linux top command documentation provides a quick method to analyze real time resource usage.
If memory saturation appears repeatedly, increasing container limits or optimizing object allocation might resolve the issue. But sometimes engineers increase limits without analyzing leaks first. That only delays the problem.
Fix #6 Token Authentication Synchronization
Distributed authentication systems sometimes fall out of sync. When one server validates tokens using a slightly different timestamp reference than another server, requests fail.
That mismatch can trigger the 2579xao6 code bug in microservice environments.
Solutions usually involve:
- Synchronizing server clocks with NTP services
- Verifying JWT expiration policies
- Aligning authentication middleware versions
Clock drift is a weird issue because it seems impossible at first. But when servers run across different cloud regions the drift happens more often than many expect.
Fix #7 Emergency Rollback to the Previous Stable Build
If the bug appears right after deployment, the fastest rescue method may simply be rolling back.
Developers sometimes resist rollback because they believe the new version must work. But stability matters more than pride. Returning to a stable build gives engineers breathing room to investigate.
Deployment systems like blue green pipelines make rollbacks safer and faster. Once traffic returns to the stable version, debugging becomes far less stressful.
And honestly, debugging while production is burning feels horrible. Everyone in the team gets tense, mistakes increase, communication gets messy. A rollback cools everything down.
Long Term Prevention Strategies
Fixing the 2579xao6 code bug once does not guarantee it will never return. Preventive engineering practices reduce future incidents dramatically.
Recommended long term habits include:
- Automated integration testing across environments
- Continuous dependency auditing
- Scheduled database integrity checks
- Centralized logging for all services
Engineers who adopt strong observability practices detect anomalies before they grow into system wide failures. The bug rarely arrives without warning signs. Logs whisper clues early, but someone must be paying attention.
Final Thoughts
The 2579xao6 code bug has earned a reputation for confusion, yet most of its causes are surprisingly ordinary. Configuration conflicts, dependency mismatches, memory limits, or authentication drift usually sit at the center of the problem.
By approaching debugging methodically and applying the seven fixes outlined above, teams can restore stability quickly. Some solutions may feel almost too simple. Still, those simple checks have saved countless production environments from extended outages.
Software failures will always exist. What matters is how quickly we recognize patterns, test solutions, and restore trust in the systems people depend on every day.